One of the many new services re-invented at AWS’s re:invent conference was the storage of secrets for applications. Secrets in essence are generally things your application may need to run but you don’t really want to put in source control. Things like API keys, password salt, database connection strings and the like.
Current ways of providing secrets to applications are things like configuration files deployed separately, Heroku’s config which exposes them as environment variables, HashiCorp Vault, CloudFormation variables, and plenty of other solutions. AWS already had a dedicated mechanism for storing secrets and making them available via an API call in it’s SSM Parameter Store service, in which you could store values, with optional encryption.
AWS Secrets Manager is slightly but not very different from SSM Parameter Store; it adds secret rotation capabilities and isn’t as buried deep down inside the obliquely named “AWS Systems Manager” service. I think those are the main features. Oh it also lets you package a set of key/value pairs into one secret, whereas Param Store makes you create separate values that require individual API calls to retrieve.
Using Secrets With Serverless
To store encrypted secrets in the AWS Secrets Manager and make them available to your serverless application, you need to do the following:
- Create a secret in Secrets Manager. Select “Other type of secrets” unless you are storing database connection info, in which case click one of those buttons instead.
- Select an encryption key to use. Probably best to create a key per application/stage.
- Create key/value pairs for your secrets.
- After creating the secret, there will be sample code for different languages that shows you how to read it in in your application.

Encryption Key Access
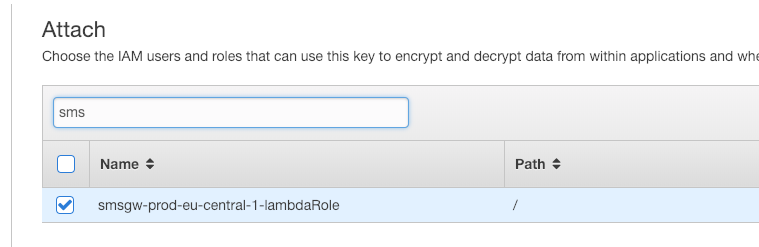
To create encryption keys, look in IAM (click “Encryption Keys on the bottom left in IAM) and assign admins and users of the keys. I manually assign the lambda role that’s been created as a user of the encryption key it needs access to in the console. There may be a way to automate this but it feels like an appropriate step to have some small manual intervention.
IAM Role
In addition to granting your lambda role access to decrypt your secret, you also need to grant it the ability to access your secret.:
plugins:
- serverless-python-requirements
- serverless-pseudo-parameters
provider:
name: aws
runtime: python3.7
stage: ${opt:stage, 'dev'} # default to dev if not specified on command-line
iamRoleStatements:
- Effect: Allow
Action: secretsmanager:GetSecretValue
Resource: arn:aws:secretsmanager:#{AWS::Region}:#{AWS::AccountId}:secret:myapp/${self:provider.stage}/*
environment:
LOAD_SECRETS: true
This is taken from my serverless.yml file. Note the secret:myapp/dev/* bit – it’s a good idea to use prefixes in your key names so that you can restrict access to resources by stage (i.e. dev only has access to dev secrets, prod only has access to prod secrets). In general prefixing AWS resources with application/stage identifiers is a crude but readable and simple way to create IAM policies for access groups of related resources.
serverless-pseudo-parameters is a handy plugin that lets you interpolate things like AWS::Region in your configuration so that you don’t need to do an unwieldy CloudFormation Fn::Join array to generate the ARN.
Reading Secrets In Your Application
Now that your application has access to GetSecretValue and is a user of the encryption key used to encrypt your secrets, you need to access the secrets in your application.
Sample code is provided in the Secrets Manager console to read your secret. One thing to note is that if you store key/value pairs in your secret, which is most likely what you’ll want to do almost all the time, you get it back as JSON. The sample code provided doesn’t decode it. The general idea is something like:
import boto3
import base64
import json
def get_secret(secret_name):
"""Fetch secret via boto3."""
client = boto3.client(service_name='secretsmanager')
get_secret_value_response = client.get_secret_value(SecretId=secret_name)
if 'SecretString' in get_secret_value_response:
secret = get_secret_value_response['SecretString']
return json.loads(secret)
else:
decoded_binary_secret = base64.b64decode(get_secret_value_response['SecretBinary'])
return decoded_binary_secret
And then you can do as you please with the secrets.
App Configuration
I like consuming secrets directly into my application’s configuration at startup. With Flask it looks something like this:
if os.getenv('LOAD_SECRETS'):
# fetch config secrets from Secrets Manager
secret_name = app.config['SECRET_NAME'] # dev, prod
secrets = get_secret(secret_name=secret_name)
if secrets:
log.debug(f"{len(secrets.keys())} secrets loaded")
app.config.update(secrets)
else:
log.debug("Failed to load secrets")- First, only try to load secrets if we’re executing under serverless/lambda. LOAD_SECRETS is defined as true in the serverless.yml snippet above. This should not be true when running tests, as you don’t want tests to access secrets and you don’t want to pay for all the additional accesses anyhow.
- SECRET_NAME is in application config and can be different for dev and prod.
- app.config.update(secrets) adds whatever you stored in Secrets Manager to your app config.
- I should probably make a dumb PyPI module to do this automatically.